Introduction
OpsRamp provides you with the capability to build your integration using the Custom SSO Integration framework.
Custom SSO integration is configured between OpsRamp and your application if any third-party or other in-house applications are not present in the Available Integrations list.
SSO integration configuration involves your application and OpsRamp platform to configure redirects to your custom branding URL.
Prerequisites
- SAML EndPoints for HTTP
- x.509 Certificate (metadata XML file)
- Identity provider Issuer URL
- Logout URL
Configure Custom (SSO) integration
Follow these steps to configure Custom (SSO) integration:
Click All Clients, select a client.
Click Setup > Account.
Select the Integrations tile.
The Installed Integrations screen is displayed, with all the installed applications. Click + ADD on the Installed Integrations page.
If you do not have any installed applications, you will be navigated to the Available Integrations page. The Available Integrations page displays all the available applications along with the newly created application with the version.
Note: Search for the application using the search option available. Alternatively, use the All Categories option to search.Click +ADD on the Custom (SSO) tile.
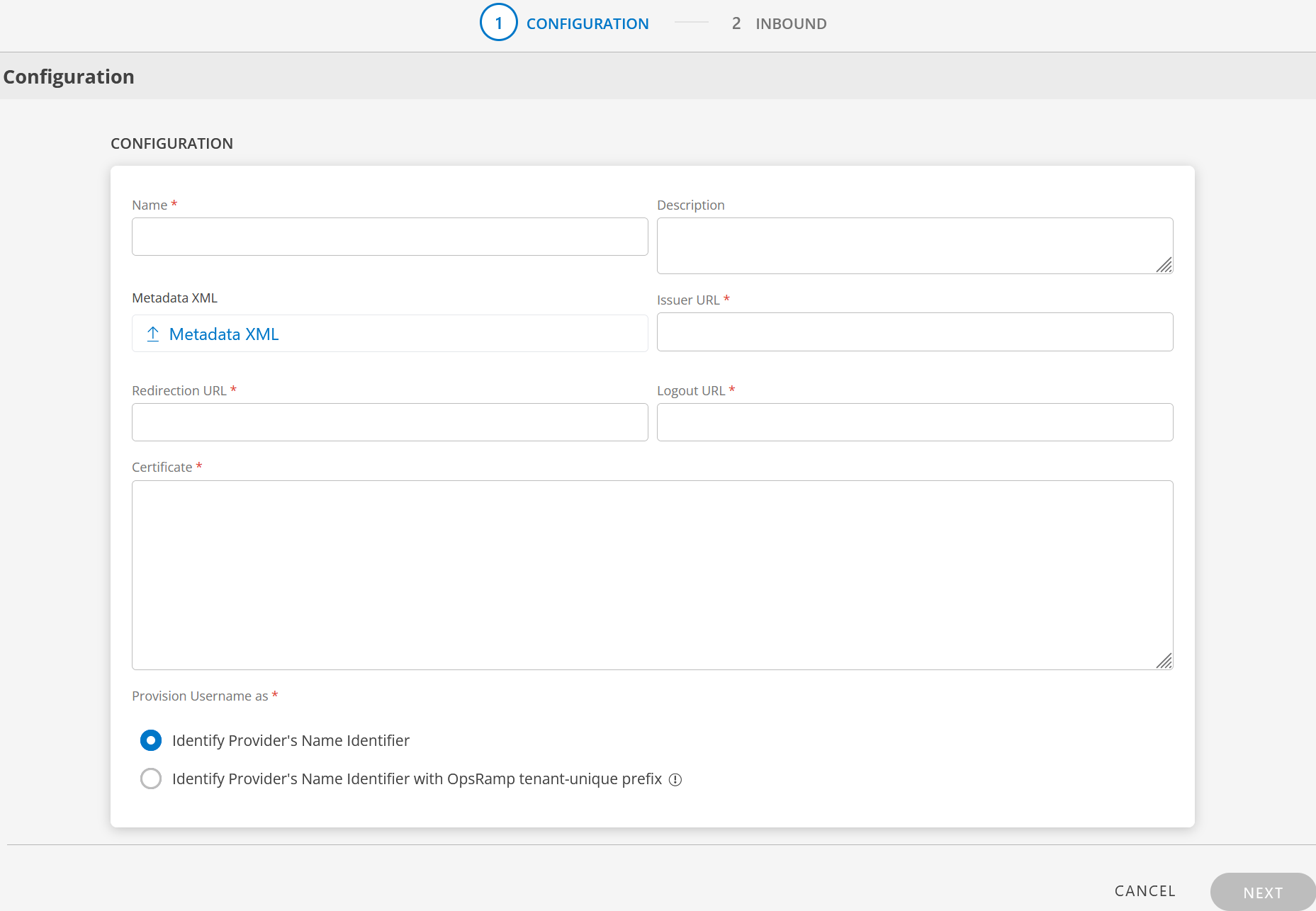
Enter the following information in the Configuration screen:
CONFIGURE
Field Name Field Type Description Name String Enter a unique name for the integration. Description String Provide a description for the integration. Metadata XML File input Upload the XML file. This file will have all the information related to Issuer URL, Redirection URL, Logout URL, and Certificate.
After you upload the Metadata XML file, these fields are automatically populated.
Alternatively, you can enter the information in the fields manually.Issuer URL String Identity provider Issuer URL. Redirection URL String SAML EndPoints for HTTP. Logout URL String URL for logging out. Certificate String x.509 Certificate Provision Username as
There are two ways to provision a user. Select the appropriate option.Radio button Identify Provider's Name Identifier
option is selected by default. The user which is created in the SSO portal will reflect in OpsRamp.
Identify Provider's Name Identifier with OpsRamp tenant-unique prefix
This option allows you to:- Create usernames with a unique 3-digit alphanumeric prefix, that is generated automatically by the system.
- Install the same identity provider across multiple OpsRamp tenants.
Note: Once you enable this option and install the integration, you cannot revert your changes. Example: There are three partners, Partner P1, P2, and P3. Each partner has usernames created with unique 3-digit alphanumeric prefix, like g0z.username1 for partner P1, p0w.username1 for partner P2, and t9q.username1 for partner P3.
Click Next. The INBOUND screen is displayed.
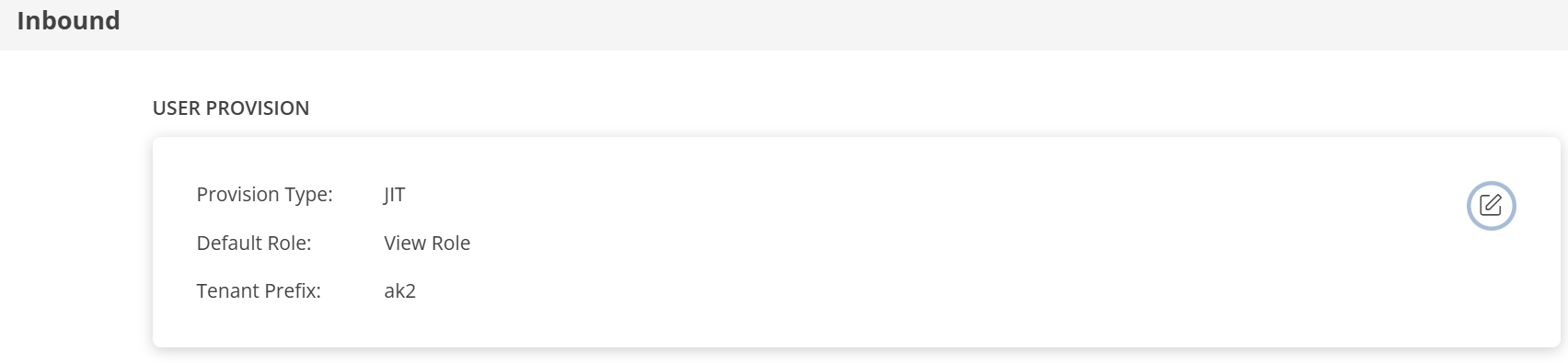
In the Inbound page, there are two sections: USER PROVISION and MAP ATTRIBUTES.
USER PROVISION
- JIT
- NONE: Only the existing users will be able to login.
JIT
Following section describes JIT provisioning in detail.
In the Inbound page:
- Click the edit icon, enter the following information, and click UPDATE USER PROVISION:
Field Name Field Type Description Provision Type Dropdown Select provision type as JIT.
When configuring the integration it is necessary to select the Provision Type - JIT to synchronize users when provisioning occurs.Default Role Dropdown The required user role. 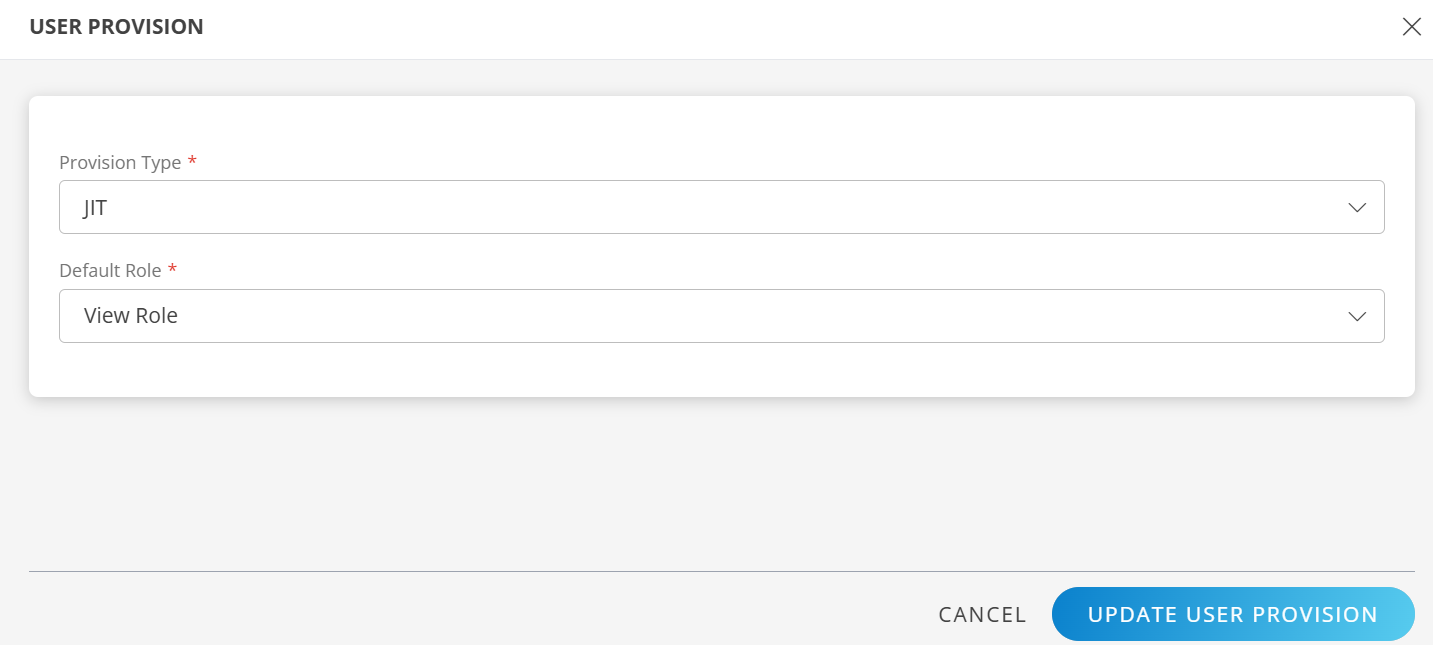
The details are updated and the USER PROVISION section displays the unique Tenant Prefix. These details are used when configuring custom SSO Provisioning settings.
MAP ATTRIBUTES
Define the following Map Attributes:
Note:
- For JIT: The OpsRamp properties like Primary Email, First Name, Last Name, and Role are required.
- Click +Add in the Map Attributes section.
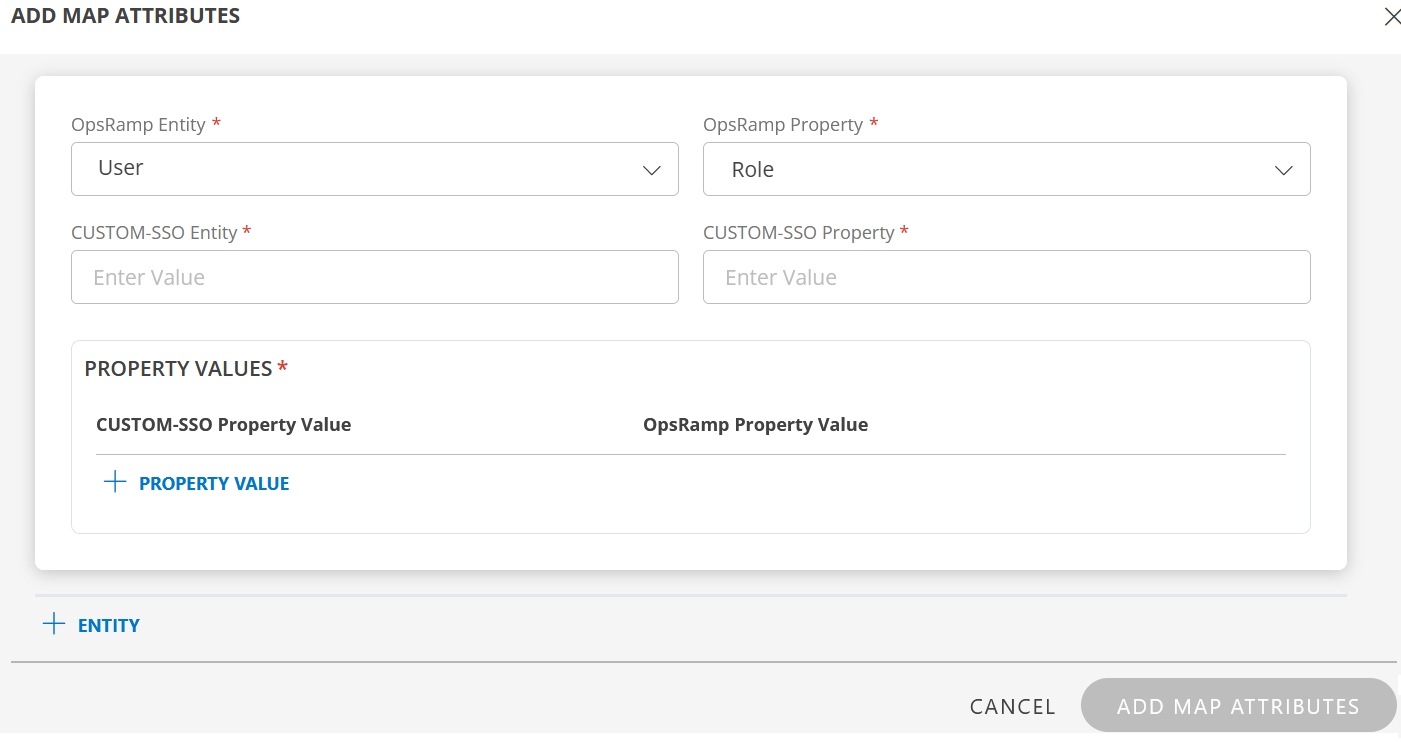
- From the Add Map Attributes window, enter the following information:
User:
- Select OpsRamp Entity as User and OpsRamp Property as Role.
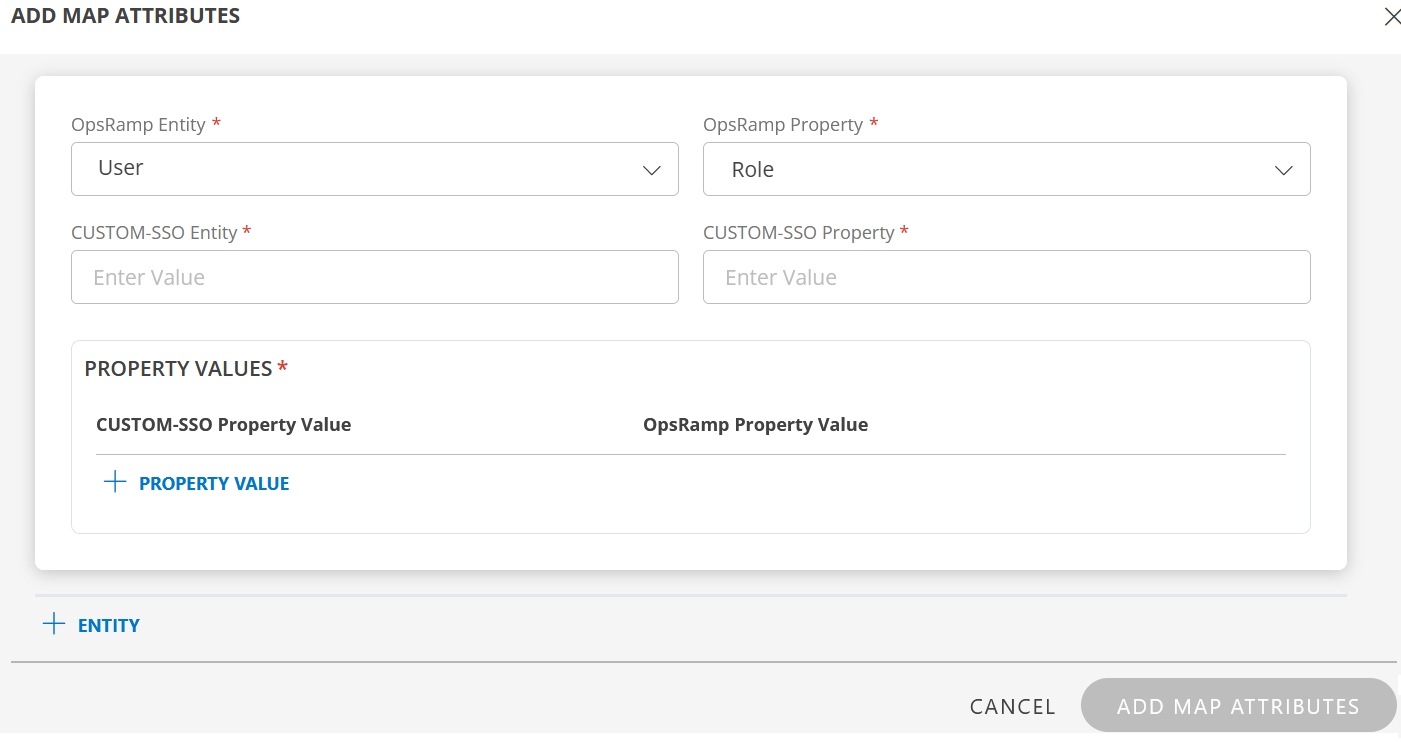
- CUSTOM-SSO Entity: Enter the value.
- CUSTOM-SSO Property: Enter the value.
In PROPERTY VALUES: section - CUSTOM-SSO Property Value: Enter the Custom-SSO property value.
- OpsRamp Property Value: Select the appropriate role corresponding to the CUSTOM-SSO Property Value.
- Click Save. The mapping is saved and displayed.
To add more property values click +Property Value.
User the Filter option to filter the map attributes.
Similarly, map attributes for other entities.
Note: If mapping for Time Zone is not provided, then organization timezone is considered by default.
- Click ADD MAP ATTRIBUTES.
- Click the three dots (menu icon) available at the end of each row to edit or delete a map attribute.
- Use Filter to filter the map attributes.
Note: If Role is not configured in Map Attributes section, the Default Role provided in USER PROVISION section is considered for SSO.
- For JIT: The OpsRamp properties like Primary Email, First Name, Last Name, and Role are required.
Click FINISH. The custom SSO integration is installed and displayed under Installed Integrations.
Actions on Integration
You can perform actions like View Logs, Export, Edit, and Uninstall on the integration.
- See Actions on Integration for more information.
Audit Logs
View Inbound logs from the View Logs option for the integration. You can view if the event was successful or not.
See Audit Logs for more information.